The Top 10 Things Every Lawyer Must Know About Computer Forensics
Computer Forensic, Cybersecurity and Managed IT Solutions.
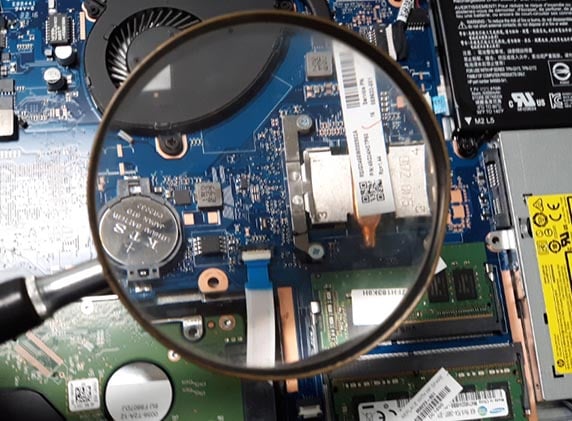
Computer Forensics (often referred to as Digital Forensics) is a branch of forensic science that involves the collection, recovery, and investigation of data found on devices and accounts that store electronic data. Common devices that are the subject of digital forensic analysis include personal computers, laptops, tablets, smart phones, servers, email accounts, social media accounts, web-based storage accounts, wearable technology, and Internet connected devices (Internet of Things), among others.
Today, Computer Forensics is used by leading attorneys and is often the key to a successful legal outcome. Every lawyer should know the following:
- Maintaining a proper Chain of Custody if critical. Maintain a record of how and when each device was collected, as well as the make, model and serial number of each device.
- “Deleted files” most often times can be recovered. Items such as deleted files, deleted browsing history, deleted instant messages, deleted texts, deleted photos, etc. are usually recoverable by a skilled certified computer forensic examiner.
- Think Broadly. When preserving, collecting, and analyzing electronic evidence, whether in anticipation of litigation or as part of an investigation, think broadly. In addition to collecting devices like computers, tablets, phones, and hard drives, consider Digital Forensics for items such as security camera footage, key card access logs, printer logs, car entertainment systems, server or database logs, etc.
- Making a forensically sound image before anyone touches the device is critical. It’s essential that an exact byte-for-byte copy (image) is created of the source device. This image needs to be made BEFORE anyone takes any investigative steps, because seemingly innocuous actions can change the data that exists on the device, thereby creating question about whether the evidence can be trusted.
- Turning on or off a computer can lose evidence. Every time you turn on or off a computer, the operating system alters the files during the startup or shutdown procedure. And, if any data is stored in the temporary memory called RAM, this data is lost with power to the device ends.
- Use of external devices. Some devices, such as an external hard drive or USB drives leave behind clues as to what the user did. A computer forensic expert can generate a list of those external devices that were connected to the source device, showing the date, time, and serial number of the external device.
- Timestamps. Piecing together a timeline of events is often key to any investigation or litigation. Digital time stamps are based on the devices internal clock.
- Virtual machines may be hiding evidence. It is possible for a user to essentially set up a computer within a computer so that he or she can run an operating system and applications covertly. This is referred to as a “virtual machine.” While virtual machines have many common and non-nefarious uses, a bad actor could use a virtual machine to bypass security measures.
- Your computer forensic expert needs background information. Factual data for the case will indicate the best places to look for the evidence or whether any other data points may be relevant. Treat your forensic examiner as part of the investigative team and give them an understating of the circumstances, background facts, and high-level legal strategy to allow the expert to effectively search the electronic data for “smoking guns” and other evidence.
- Not all certified computer forensics examiners are the same. Selecting your Digital Forensics Expert requires the same degree of scrutiny and care as you would use when selecting the right surgeon or the right lawyer. It is more art than science, and how the evidence is gathered and presented varies greatly from one firm to another.
ELIJAH has been called as an expert witness in hundreds of cases and services many of the largest law firms and corporations. We use the industry best practices to collect, preserve, and examine digital evidence. Our experts can quickly and efficiently find key issues and areas of concern for examination. ELIJAH’s experts handle evidence in criminal and civil cases with a track record of testifying persuasively in support of these approaches.
About ELIJAH
Founded in 2003, ELIJAH is a multi-award-winning leader in providing expert digital forensic, data security solutions, and managed IT. ELIJAH is owned and managed by former litigation partners and is an efficient boutique digital forensic, cybersecurity and IT solutions provider that makes clients’ lives easier through effective communication and white glove service. For additional information, please visit https://www.elijaht.com or call 866-354-5240.





























